Boosted by GenAI in the world of technology, code development has been vastly improved with efficiency without necessarily compromising originality. Nevertheless, behind all the wonders of automated coding stands a silent but important concern - the oversight of weak links within GenAI-created code. The Promise of GenAI-Generated Code GenAI's learning tool, which can imitate...
Blog

In the ever-evolving software development landscape, the symbiotic relationship between DevOps and containerization has revolutionized how applications are built, deployed, and managed. DevOps practices emphasize speed, collaboration, and continuous delivery, while containers provide consistency and portability across different environments. However, this dynamic duo is incomplete without a critical aspect: security. Container security is pivotal in...

Ensuring the security and integrity of data is paramount in the dynamic world of software development. One crucial aspect of this is the handling of URLs, which involves encoding and decoding to prevent data corruption and vulnerabilities. In this blog post, we will delve into URL encoding and decoding in Java, exploring the importance of...

Software plays a vital role in our daily lives, powering everything from smartphones to critical infrastructure. However, this reliance on software also brings potential risks, such as security vulnerabilities and supply chain complexities. To address these challenges, the Software Bill of Materials (SBOM) concept has emerged as a powerful tool to enhance software security, transparency,...
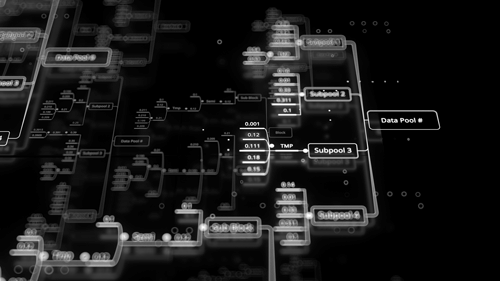
Businesses and organizations rely heavily on the seamless information flow to make critical decisions, optimize processes, and enhance customer experiences. However, data loss can be catastrophic, leading to financial losses, damaged reputation, and even regulatory repercussions. Choosing the exemplary data architecture is a fundamental step in ensuring the security and resilience of your data. Today,...

With the growth of technology, AI and cybersecurity have engendered questions about threats that may come from the use of artificial intelligence. In trying to get into details on this complex dance, we must analyze and determine whether AI threatens cybersecurity or functions as a beneficial ally. The Dual Nature of AI in Cybersecurity...
The cloud-native revolution has transformed how we develop and deploy applications. Infrastructure as code (IaC) and containerization with technologies like Docker and Kubernetes have become foundational elements for building and managing modern software systems.
