Businesses and organizations rely heavily on the seamless information flow to make critical decisions, optimize processes, and enhance customer experiences. However, data loss can be catastrophic, leading to financial losses, damaged reputation, and even regulatory repercussions.
Choosing the exemplary data architecture is a fundamental step in ensuring the security and resilience of your data. Today, we will explore the importance of data architecture and critical considerations for preventing data loss.
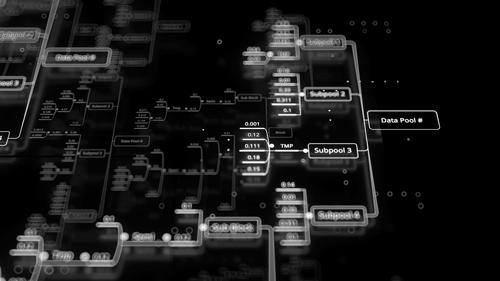
Data Architecture: A Foundation for Resilience
Data architecture refers to a data management system's overall structure and design. It encompasses the organization, storage, integration, and access to data across an organization. A well-designed data architecture provides several benefits; data loss prevention is a primary advantage.
- Data Redundancy: Redundancy involves creating and storing multiple copies of data in separate locations. In case of a hardware failure or other disaster, redundant data copies ensure a backup to restore critical information, thereby reducing the risk of data loss.
- Scalability: As businesses grow, the volume of data they handle also expands. A scalable data architecture can accommodate this growth seamlessly, without compromising the integrity of the data or increasing the chances of data loss.
- Disaster Recovery: An effective data architecture includes provisions for disaster recovery strategies. Regular data backups and real-time replication to remote locations can minimize data loss in a natural disaster or cyber-attack.
Key Considerations for Preventing Data Loss
Now that we understand the importance of data architecture in data loss prevention let's delve into the key considerations when choosing the right architecture for your organization:
1. Data Backup and Recovery Strategy:
- Regular Backups: Implement a robust backup strategy that ensures regular and automated backups of your critical data. The frequency of backups should align with your business needs and data volatility.
- Backup Storage: Consider storing backups in secure off-site locations, such as cloud-based services or physically isolated data centers. This redundancy protects against data loss due to physical damage or local disasters.
- Testing Restoration: Periodically test the restoration process from backups to verify the data integrity and ensure the recovery process is effective.
2. Data Security:
- Encryption: Prioritize data encryption both in transit and at rest. Strong encryption ensures that even if unauthorized individuals gain access to the data, it remains incomprehensible to them.
- Access Controls: Implement role-based access controls to limit data access only to authorized personnel. This minimizes the risk of accidental or intentional data tampering or deletion.
- Monitoring and Auditing: Regularly monitor data access and changes to detect suspicious activities. Conduct periodic audits to ensure compliance with data security policies and regulations.
3. High Availability:
- Redundancy and Failover: Employ redundant hardware and systems to ensure high availability. Implement failover mechanisms that automatically switch to backup resources if the primary ones fail, thereby minimizing service interruptions and data loss.
- Load Balancing: Distribute data across multiple servers and resources to prevent overload and ensure continuous access and availability.
4. Disaster Recovery Plan:
- Risk Assessment: Conduct a thorough risk assessment to identify potential threats and vulnerabilities to your data. This will help craft a comprehensive disaster recovery plan tailored to your organization's needs.
- Business Continuity: Define recovery point objectives (RPOs) and recovery time objectives (RTOs) to establish how much data loss and downtime your business can tolerate during a disaster.
- Test and Update: Regularly test your disaster recovery plan and update it as your organization evolves. Periodic drills and simulations will help ensure your team is prepared to execute the plan effectively.
5. Cloud-Based Solutions:
Cloud-based data architectures offer several advantages in preventing data loss:
- Automatic Backups: Many cloud services offer automatic backups, reducing the burden on your team to manage backups manually.
- Geographic Redundancy: Reputable cloud providers maintain data centers in multiple geographic regions, providing inherent redundancy and disaster recovery capabilities.
- Scalability: Cloud solutions can quickly scale to accommodate data growth without requiring significant upfront investments.
Preventing data loss is paramount for every organization seeking to thrive in today's data-centric landscape. Investing in the right data architecture protects you from data loss and empowers your organization to leverage its data effectively, making informed decisions and staying competitive in the digital age. Remember, data loss prevention is not an afterthought; it's an essential aspect of building a resilient and successful business.



No Comments Available...