Modern security tools provide a variety of implementation options including full-function clients, APIs and CI/CD plugins. What is the best option for you? The answer to that depends on your role and how you will use the tools. Are you doing software development, security, or management?
For software developers, integrating security inside their CI/CD tools is the preferred approach because of automation, signal value, and reduced friction.
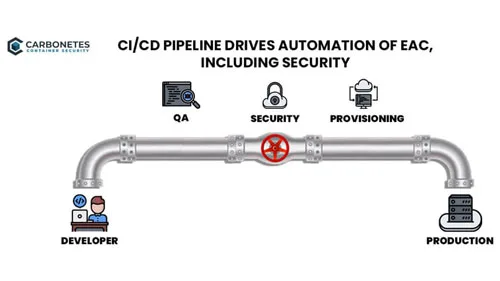
CI/CD & Automation
Automation is a key benefit that drives adoption of CI/CD toolchains. DevOps, DevSecOps, GitOps, all of these are enabled or enhanced by CI/CD workflow automation. By automating security analysis and policy evaluation inside the CI/CD workflow and triggering it after build, it becomes a natural part of the developer’s workflow. This greatly enhances both efficiency and compliance.
Signal Value
The results from security analysis and policy evaluation send a valuable signal to the developer, indicating which packages or dependencies are vulnerable/compromised before their work on that docker image is complete. You want this as close to the development process as possible. For example, you could implement security in the Kubernetes admission controllers, but then the signal is often presented to the wrong person, operations, at the wrong time. You then rely on signal routing tools like bug tracking or collaboration tools, but they also delay delivery of that signal to the developer. Implementing security upon container check-in brings it closer to the developer, but for immediate feedback while the code is top of mind, running security analysis and policy evaluation at build is ideal.
Reduced Friction
If developers are forced to exit their CI/CD workflow to get results from security and policy analysis you introduce friction to adoption and use. Adoption friction is caused by the need to learn a new tool, most developers don’t want to take time away from their work to learn new tools. There is also friction in using a separate tool. The developer has to switch out of their development tools into a security tool. This causes friction each time. It compounds if there are multiple tools they must use outside of their normal CI/CD workflow. This friction can result in developers forgetting these steps, so compliance drops along with efficiency. Integrating security and policy evaluation right inside the CI/CD platform is the most efficient approach and results in far higher compliance.
Conclusion
For developers, integrating security and policy evaluation as CI/CD plugins is far more efficient and dramatically increase compliance. It also paves the way for secure GitOps, where the GitOps process involves security and policy evaluation. However, the beautiful and highly functional security clients are not wasted. They serve the other roles: security and management. Security people use the full function client to import, create, test and deploy policies, in addition to monitoring compliance and governance. The full-featured client is also ideal for management who can monitor overall security progress as well as using asset management tools which provide visibility into everything about their containerized code. While full-featured clients serve a vital purpose, developers prefer CI/CD plugins because they automate the entire process inside their existing workflows.



No Comments Available...