Blogs
Read our latest blog for insightful tips and knowledge!
Filter by

What's Next for IaC and Cloud-Native Container Security in 2024?
The cloud-native revolution has transformed how we develop and deploy applications. Infrastructure as code (IaC)…
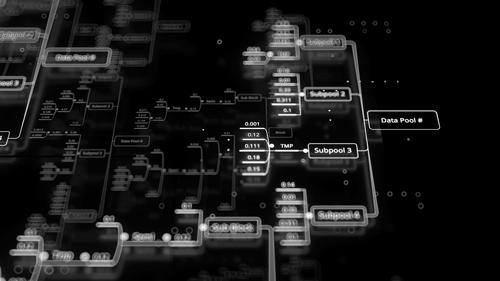
Safeguarding Your Data: Choosing the Right Architecture to Prevent Data Loss
Businesses and organizations rely heavily on the seamless information flow to make critical decisions, optimize…
The Key Benefits of Kubernetes in Container Management
Containerization has become an increasingly popular solution for organizations looking to deploy applications quickly and…

Using IaC to Manage Edge Computing Infrastructure
Edge computing is the distribution of computing power and data storage closer to where data…
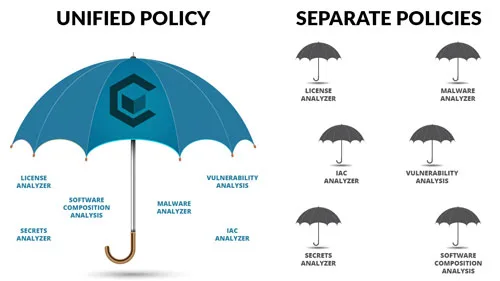
Choosing the Right Security Policy Solution
Security policies are a critical component of your security solution and selecting the right security…
5 Container Security Trends to Watch Out For in the Near Future
In the next few years, we will see a continued increase in the use of…

Safeguarding Your Code: A Comprehensive Guide to Penetration Testing Tools for Development Security
With sensitive data and valuable information being stored and processed within applications, ensuring development security…
Enhancing Container Security with Carbonetes - Lite App: A Comprehensive Overview
Container security plays a crucial role in safeguarding sensitive data and preventing potential vulnerabilities in…
Why BOM Diggity is the Superior Container Security Platform
In an era where software security is a top concern, organizations must prioritize measures to…

Enhancing Cloud Security Like No Other with BrainIAC
In the dynamic landscape of cloud computing, security remains a paramount concern. As organizations increasingly…
