Blogs
Read our latest blog for insightful tips and knowledge!
Filter by

Container Security: Comprehensive Analysis vs. Specialty Analyzers
Securing a container involves analyzing for a variety of potential risks over a variety of…
The Importance of Infrastructure as Code Analysis (IaC) in Container Security
When it comes to container security, many organizations focus on the host server or cluster.…
Infrastructure as Code (IaC) Auto-Remediation
Infrastructure as Code (IaC) is not as simple as some other security risks because IaC…
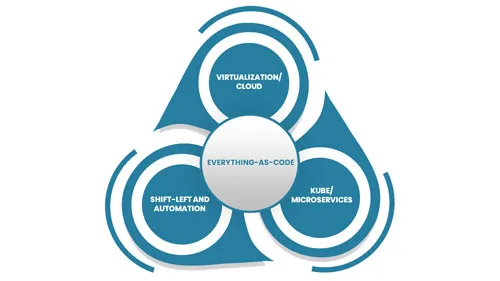
Everything-as-Code
Everything-as-Code (EaC) is the future of IT; the benefits are simply overwhelming. EaC is the…
5 Container Security Trends to Watch Out For in the Near Future
In the next few years, we will see a continued increase in the use of…

The Parties Involved in Container Threat Model
Containerized applications are the cornerstone of modern software architectures. However, the complexity and dynamism of…

Continuous Monitoring in Container Security: Safeguarding Your Digital Ecosystem
Security is paramount in the containerized applications landscape, where agility meets complexity. Traditional security measures…

Embracing Zero Trust: A Paradigm Shift in Container Security for Web Applications
Security remains a paramount concern. Traditional security models are often insufficient to combat the sophisticated…

The Importance of SBOMs in Managing IoT Software Security
Building with open-source software is essential for many IoT developers. Open-source software provides a wealth…

Using IaC to Manage Edge Computing Infrastructure
Edge computing is the distribution of computing power and data storage closer to where data…
