Blogs
Read our latest blog for insightful tips and knowledge!
Filter by

4 Advantages of Cloud-Native Container Security
Cloud-native container security is a security model that focuses on protecting containers and the microservices…
Creating Effective Docker Images with the Help of Container Security
There are times Docker images are created without much thought to security. However, given the…

Containerized Deployment Strategies for DevOps Teams
Containerization is changing the way that DevOps teams approach application deployment. By providing a portable,…

The Best Docker Alternatives That You Should Check Out!
Docker is not the only containerization tool out there. In fact, there are several great…

Why You Need To Take Advantage of The Free Trials For Container Security Management
Container security is one of the most important aspects of running a business today. With…
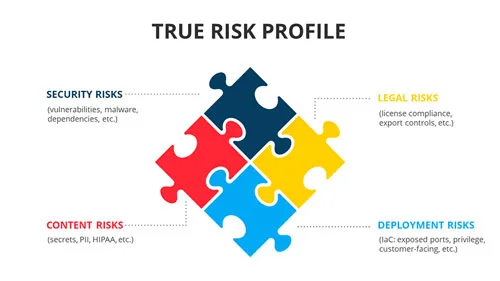
Container Security Asset Management
Container security is the practice of correlating all inherent security risks in conjunction with the…
Keeping Your Docker Secrets a Well-Kept Secret
Docker Secrets are config files that contain sensitive information, like passwords, tokens, and keys. Unlike…

The Importance of Container Runtime
When you talk about container security, a critical component inevitably comes up: container runtime. But…
The Importance of Constant Container Security Scanning
The age of containerization has ushered in a new era of container security: one where…

Why AWS Misconfiguration Should Be Avoided at All Cost
When securing your business online, no one does it like AWS (Amazon Web Services). With…
